
Lazarus hackers used fake DeFi game to exploit Google Chrome zero-day
The North Korean Lazarus hacking group exploited a Google Chrome zero-day tracked as CVE-2024-4947 through a fake decentralized finance (DeFi) game targeting individuals in the cryptocurrency space.
Kaspersky discovered the attacks on May 13, 2024, and reported the Chrome zero-day flaw to Google.
Google issued a fix for CVE-2024-4947 on May 25, with Chrome version 125.0.6422.60/.61.
Lazarus tank games
Kaspersky discovered the campaign, which started in February 2024, after detecting a new variant of the “Manuscrypt” backdoor malware on the personal computer of one of its customers in Russia.
Lazarus has been using Manuscrypt for years, but the researchers were intrigued by the threat actor’s atypical targeting scope, which seemingly included random individuals.
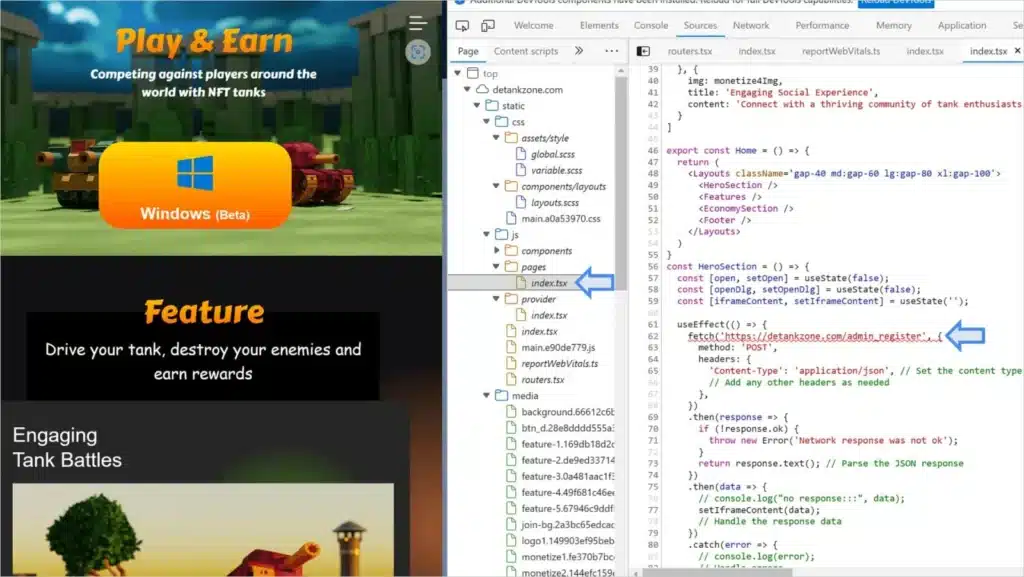
Further telemetry showed that Google Chrome was exploited prior to the detection of the new Manuscrypt payload, with the exploitation originating from the “detankzone[.]com” website. This website promoted an NFT-based multiplayer online battle arena (MOBA) game themed around tanks named DeTankZone.
Lazarus promoted the game heavily through advertising campaigns on social media platforms like X, spear-phishing emails, and premium LinkedIn accounts used in direct attacks on high-value targets.
Upon downloading and reserve engineering the game, Kaspersky discovered the game was based on stolen source code from a legitimate game named DeFiTankLand, which Lazarus had simply rebranded for their purposes.
The 400MB ZIP download launches as expected, but it does not work past the login/registration screen as the backend infrastructure for the game was shut down. Furthermore, it did not perform any malicious actions on the target’s system.
The Google Chrome exploitation happens on the detankzone[.]com website itself, which contained a hidden script (index.tsx) designed to trigger an exploit for CVE-2024-4947, a type confusion in V8, Chrome’s Javascript engine.
Lazarus’ exploit script corrupted Chrome’s memory by leveraging the app’s JIT compiler, Maglev, overwriting sections that eventually gave them access to the entire address space of Chrome’s process.
At this stage, the attackers could access cookies, authentication tokens, saved passwords, and browsing history.
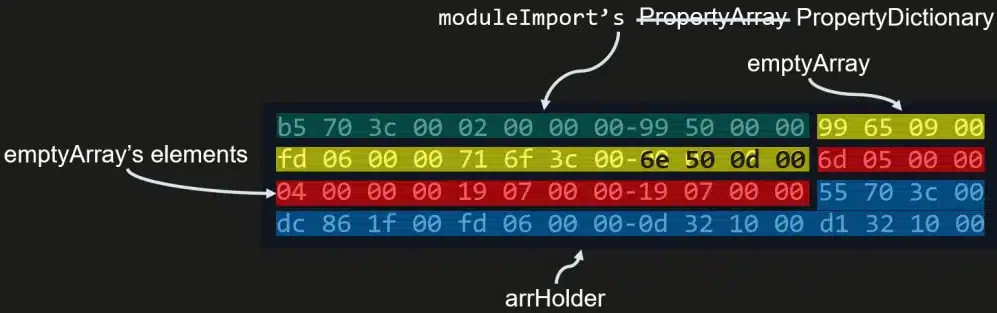
Chrome’s V8 sandbox isolates JavaScript execution from the rest of the system, so Lazarus used a second flaw in V8 to escape it and achieve remote code execution, executing shellcode in the system’s memory.
“This issue (330404819) was submitted and fixed in March 2024,” explains Kaspersky about the V8 escape flaw.
“It is unknown whether it was a bug collision and the attackers discovered it first and initially exploited it as a 0-day vulnerability, or if it was initially exploited as a 1-day vulnerability.”
The shellcode Lazarus used serves as a reconnaissance tool, helping the attackers determine if the compromised machine is valuable enough to continue the attack.
It collected CPU, BIOS, and OS information, performed anti-VM and anti-debugging checks, and sent the information to Lazarus’ command-and-control (C2) server.
Kaspersky did not have the chance to examine the subsequent attack steps, as, by the time of their analysis, Lazarus had removed their exploit from the decoy site.
However, based on the people the malicious campaign targeted and their past history, the attack’s ultimate goal was likely to steal cryptocurrency.



