
Hackers posing as Ukraine’s Security Service infect 100 govt PCs
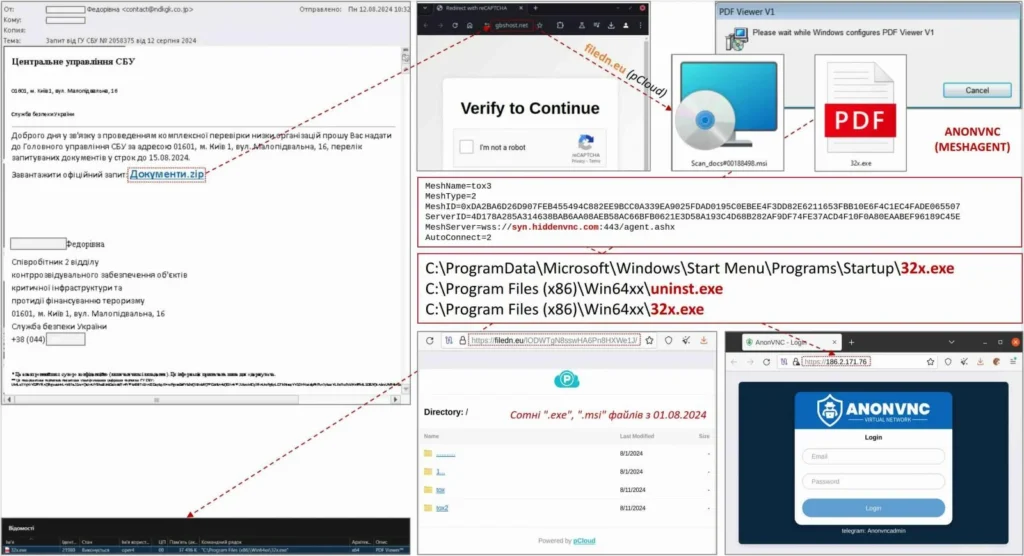
Attackers impersonating the Security Service of Ukraine (SSU) have used malicious spam emails to target and compromise systems belonging to the country’s government agencies.
On Monday, the Computer Emergency Response Team of Ukraine (CERT-UA) disclosed that the attackers successfully infected over 100 computers with AnonVNC malware.
Some samples were signed using the code signing certificate of what looks like a Chinese company (Shenzhen Variable Engine E-commerce Co Ltd).
“Good afternoon, in connection with the comprehensive inspection of a number of organizations, I am asking you to submit to the Main Directorate of the SBU at the address 01601, Kyiv 1, str. Malopodvalna, 16, list of requested documents until August 15, 2024. Download the official request: Dokumenty.zip,” the malicious emails read, linking to an attachment pretending to be a document list required by the SSU.
These attacks began over a month ago, around July 12, with emails pushing hyperlinks to a Documents.zip archive that would instead download a Windows installer MSI file from gbshost[.]net designed to deploy the malware.
While CERT-UA doesn’t provide an exact description of the malware’s capabilities, it said that it enabled the threat group tracked as UAC-0198 to access the compromised computers covertly.
“CERT-UA has identified more than 100 affected computers, in particular, among central and local government bodies,” CERT-UA said.
“Note that related cyber attacks have been carried out since at least July 2024 and may have a broader geography.”
Ukraine under attack
Last month, cybersecurity company Dragos revealed that a late January 2024 cyberattack used Russian-linked FrostyGoop malware to cut off the heating of over 600 apartment buildings in Lviv, Ukraine, for two days during sub-zero temperatures.
FrostyGoop is the ninth ICS malware discovered in the wild, with many linked to Russian threat groups. Mandiant found CosmicEnergy, and ESET spotted Industroyer2, which Sandworm hackers used in a failed attack on a Ukrainian energy provider.
In April, CERT-UA also disclosed that the notorious Sandworm Russian military hacking group targeted, and in some cases breached, 20 energy, water, and heating critical infrastructure organizations in Ukraine.
In December, Sandworm also hacked into and wiped thousands of systems on Kyivstar’s network, Ukraine’s largest telecommunications service provider. In all, as CERT-UA revealed in October, they breached the networks of 11 Ukrainian telecom service providers since May 2023.
The Main Intelligence Directorate (GUR) of Ukraine’s Ministry of Defense also claimed it hacked the Russian Ministry of Defense in March after previously claiming responsibility for breaches of the Russian Center for Space Hydrometeorology, the Russian Federal Air Transport Agency, and the Russian Federal Taxation Service.



