Proxy
TrickMo Android banker adopts TON blockchain for covert comms
A new variant of the TrickMo Android banking malware, delivered in campaigns targeting users across Europe, introduces new commands and uses The Open Network (TON) for stealthy command-and-control communications. The TrickMo banker was first spotted in September 2019 and has remained in active development, constantly receiving updates since then. In October 2024, Zimperium analyzed 40 variants of the malware […]
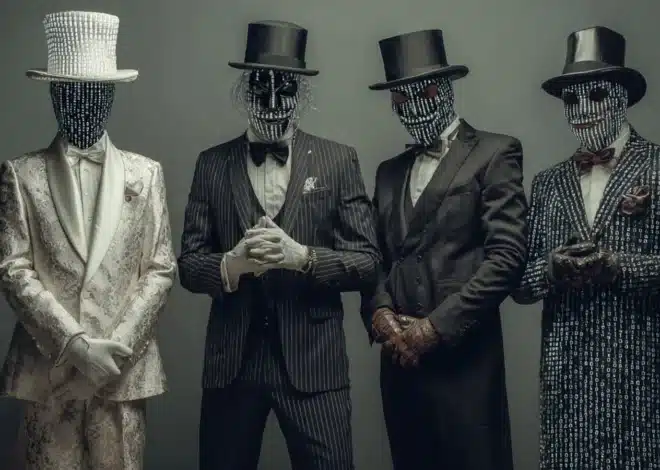
The Gentlemen ransomware now uses SystemBC for bot-powered attacks
A SystemBC proxy malware botnet of more than 1,570 hosts, believed to be corporate victims, has been discovered following an investigation into a Gentlemen ransomware attack carried out by a gang affiliate. The Gentlemen ransomware-as-a-service (RaaS) operation emerged around mid-2025 and provides a Go-based locker that can encrypt Windows, Linux, NAS, and BSD systems, and a […]
US disrupts SocksEscort proxy network powered by Linux malware
Law enforcement agencies in the U.S. and Europe, along with private partners, have disrupted the SocksEscort cybercrime proxy network that relied solely on edge devices compromised via the AVRecon malware for Linux. According to Lumen’s Black Lotus Labs (BLL), which helped the U.S. Department of Justice take down Socksescort, the proxy network had a constant average of 20,000 […]
Fake Google Security site uses PWA app to steal credentials, MFA codes
A phishing campaign is using a fake Google Account security page to deliver a web-based app capable of stealing one-time passcodes, harvesting cryptocurrency wallet addresses, and proxying attacker traffic through victims’ browsers. The attack leverages Progressive Web App (PWA) features and social engineering to deceive users into believing they are interacting with a legitimate Google […]
Malicious 7-Zip site distributes installer laced with proxy tool
A fake 7-Zip website is distributing a trojanized installer of the popular archiving tool that turns the user’s computer into a residential proxy node. Residential proxy networks use home user devices to route traffic with the goal of evading blocks and performing various malicious activities such as credential stuffing, phishing, and malware distribution. The new campaign […]
Hackers compromise NGINX servers to redirect user traffic
A threat actor is compromising NGINX servers in a campaign that hijacks user traffic and reroutes it through the attacker’s backend infrastructure. NGINX is open-source software for web traffic management. It intermediates connections between users and servers and is employed for web serving, load balancing, caching, and reverse proxying. The malicious campaign, discovered by researchers at […]
Google disrupts IPIDEA residential proxy networks fueled by malware
IPIDEA, one of the largest residential proxy networks used by threat actors, was disrupted earlier this week by Google Threat Intelligence Group (GTIG) in collaboration with industry partners. The action included taking down domains associated with IPIDEA services, infected device management, proxy traffic routing. Additionally, intelligence has been shared on the IPIDEA software development kits (SDK) […]
Hidden Telegram proxy links can reveal your IP address in one click
A single click on what may appear to be a Telegram username or harmless link is all it takes to expose your real IP address to attackers due to how proxy links are handled. Telegram tells GeekFeed it will now add warnings to proxy links after researchers demonstrated that specially crafted links could be used […]
Kimwolf Android botnet abuses residential proxies to infect internal devices
The Kimwolf botnet, an Android variant of the Aisuru malware, has grown to more than two million hosts, most of them infected by exploiting vulnerabilities in residential proxy networks to target devices on internal networks. Researchers observed increased activity for the malware since last August. Over the past month, Kimwolf has intensified its scanning of […]
Malicious extensions in Chrome Web store steal user credentials
Two Chrome extensions in the Web Store named ‘Phantom Shuttle’ are posing as plugins for a proxy service to hijack user traffic and steal sensitive data. Both extensions are still present in Chrome’s official marketplace at the time of writing and have been active since at least 2017, according to a report from researchers at the […]