
Ransomware gang deploys new malware to kill security software
RansomHub ransomware operators are now deploying new malware to disable Endpoint Detection and Response (EDR) security software in Bring Your Own Vulnerable Driver (BYOVD) attacks.
Named EDRKillShifter by Sophos security researchers who discovered it during a May 2024 ransomware investigation, the malware deploys a legitimate, vulnerable driver on targeted devices to escalate privileges, disable security solutions, and take control of the system.
This technique is very popular among various threat actors, ranging from financially motivated ransomware gangs to state-backed hacking groups.
“During the incident in May, the threat actors – we estimate with moderate confidence that this tool is being used by multiple attackers — attempted to use EDRKillShifter to terminate Sophos protection on the targeted computer, but the tool failed,” said Sophos threat researcher Andreas Klopsch.
“They then attempted to run the ransomware executable on the machine they controlled, but that also failed when the endpoint agent’s CryptoGuard feature was triggered.”
While investigating, Sophos discovered two different samples, both with proof-of-concept exploits available on GitHub: one exploiting a vulnerable driver known as RentDrv2 and another exploiting a driver called ThreatFireMonitor, a component of a deprecated system-monitoring package.
Sophos also found that EDRKillShifter can deliver various driver payloads based on the attackers’ needs and that the malware’s language property suggests it was compiled on a computer with Russian localization.
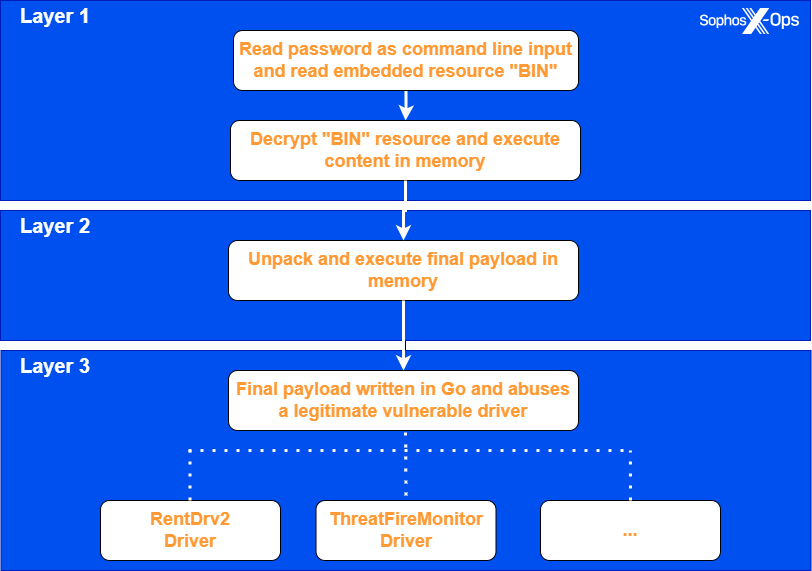
The loader’s execution involves three steps: first, the attacker launches the EDRKillShifter binary with a password string to decrypt and execute an embedded resource named BIN in memory. This code then unpacks and executes the final payload, which drops and exploits a vulnerable, legitimate driver to escalate privileges and disable active EDR processes and services.
“After the malware creates a new service for the driver, starts the service, and loads the driver, it enters an endless loop that continuously enumerates the running processes, terminating processes if their name appears in a hardcoded list of targets,” Klopsch added.
“It is also worth noting that both variants exploit legitimate (though vulnerable) drivers, using proof-of-concept exploits available on Github. We suspect that the threat actors copied portions of these proofs-of-concept, modified them, and ported the code to the Go language.”
Sophos recommends enabling tamper protection in endpoint security products, maintaining a separation between user and admin privileges to prevent attackers from loading vulnerable drivers, and keeping systems updated, given that Microsoft keeps de-certifying signed drivers known to have been misused in previous attacks.
Last year, Sophos spotted another EDR-killing malware, dubbed AuKill, which abused a vulnerable Process Explorer driver in Medusa Locker and LockBit ransomware attacks. AuKill is similar to an open-source tool known as Backstab, which also exploits a vulnerable Process Explorer driver and has been used by the LockBit gang in at least one attack observed by Sophos X-Ops.



