New stealthy Pumakit Linux rootkit malware spotted in the wild
A new Linux rootkit malware called Pumakit has been discovered that uses stealth and advanced privilege escalation techniques to hide its presence on systems.
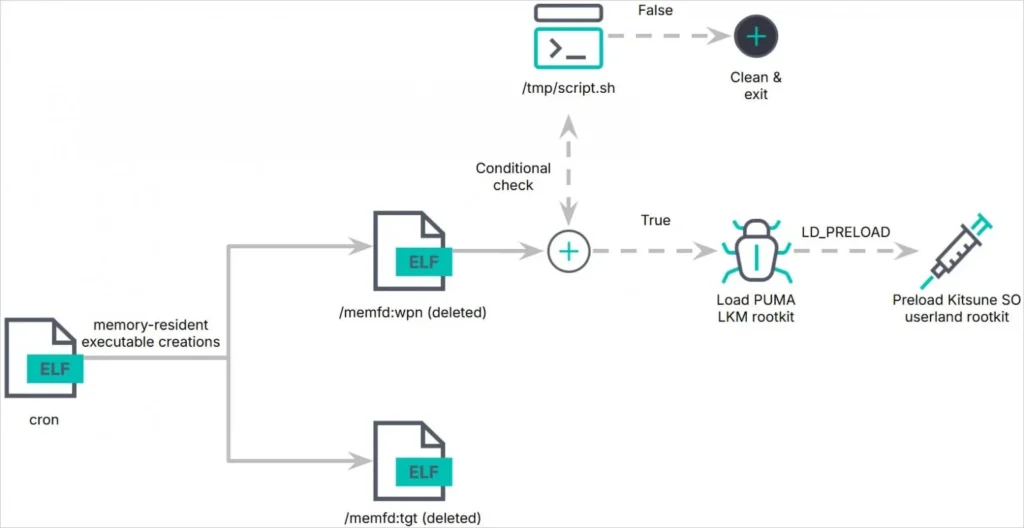
The malware is a multi-component set that includes a dropper, memory-resident executables, a kernel module rootkit, and a shared object (SO) userland rootkit.
Elastic Security discovered Pumakit in a suspicious binary (‘cron’) upload on VirusTotal, dated September 4, 2024, and reported having no visibility into who uses it and what it targets.
Generally, these tools are used by advanced threat actors targeting critical infrastructure and enterprise systems for espionage, financial theft, and disruption operations.
The Pumakit
Pumakit employs a multi-stage infection process starting with a dropper named ‘cron,’ which executes embedded payloads (‘/memfd:tgt’ and ‘/memfd:wpn’) entirely from memory.
The ‘/memfd:wpn’ payload, which executes in a child process, performs environment checks and kernel image manipulation and eventually deploys the LKM rootkit module (‘puma.ko’) into the system kernel.
Embedded within the LKM rootkit is Kitsune SO (‘lib64/libs.so’), acting as the userland rootkit that injects itself into processes using ‘LD_PRELOAD’ to intercept system calls at the user level.
Stealthy privilege escalation
The rootkit follows a conditional activation, checking for specific kernel symbols, secure boot status, and other prerequisites before loading.
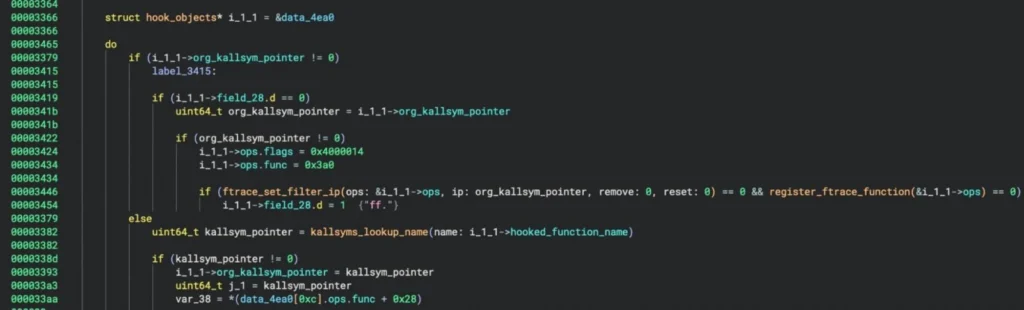
Elastic says Puma utilizes the ‘kallsyms_lookup_name()’ function to manipulate system behavior. This indicates the rootkit was designed to only target Linux kernels before version 5.7, as newer versions no longer export the function and, therefore, can’t be used by other kernel modules.
“The LKM rootkit’s ability to manipulate system behavior begins with its use of the syscall table and its reliance on kallsyms_lookup_name() for symbol resolution,” explains Elastic researchers Remco Sprooten and Ruben Groenewoud.
“Unlike modern rootkits targeting kernel versions 5.7 and above, the rootkit does not use kprobes, indicating it is designed for older kernels.”
Puma hooks 18 syscalls and multiple kernel functions using ‘ftrace,’ to gain privilege escalation, command execution, and the ability to hide processes.
The kernel functions ‘prepare_creds’ and ‘commit_creds’ are abused to modify process credentials, granting root privileges to specific processes.
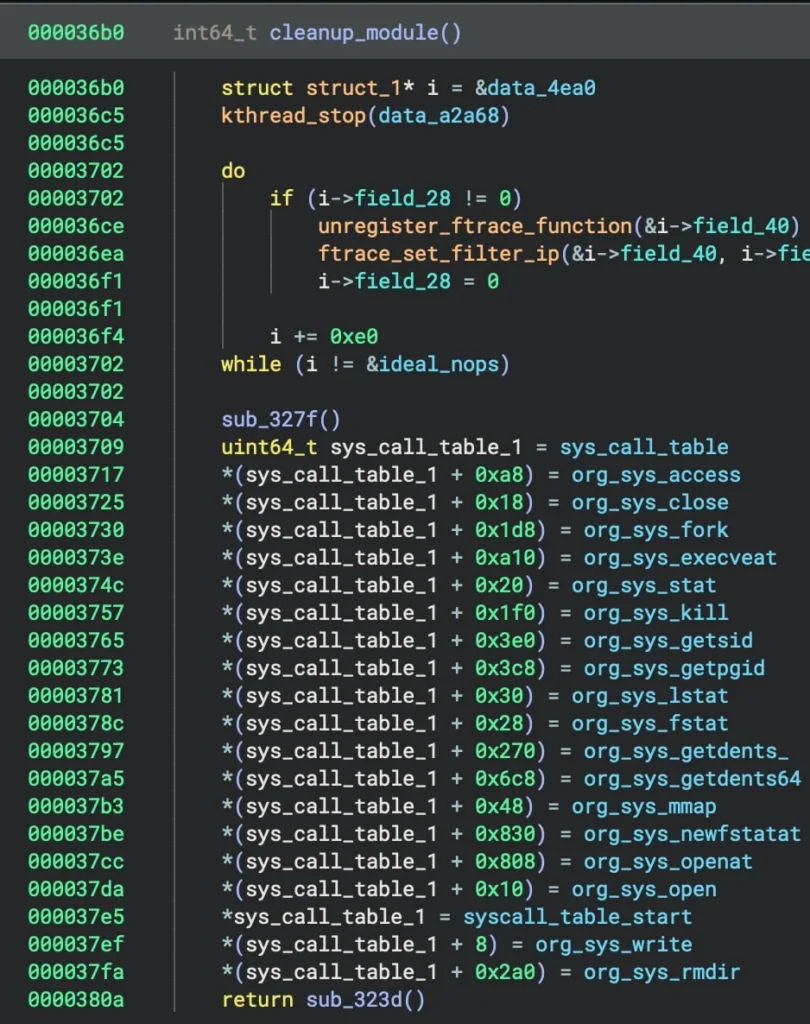
The rootkit can hide its own presence from kernel logs, system tools, and antivirus, and can also hide specific files in a directory and objects from process lists.
If the hooks are interrupted, the rootkit reinitializes them, ensuring that its malicious changes aren’t reverted and the module cannot be unloaded.
The userland rootkit Kitsune SO operates in synergy with Puma, extending its stealth and control mechanisms to user-facing interactions.
It intercepts user-level system calls and alters the behavior of looks like ls, ps, netstat, top, htop, and cat to hide files, processes, and network connections associated with the rootkit
It can also dynamically hide any other files and directories based on attacker-defined criteria and make malicious binaries entirely invisible to users and system admins.
Kitsune SO also handles all communications with the command and control (C2) server, relaying commands to the LKM rootkit and transmitting configuration and system info to the operators.
Besides file hashes, Elastic Security has published a YARA rule to help Linux system administrators detect Pumakit attacks.



