
Malware exploits 5-year-old zero-day to infect end-of-life IP cameras
The Corona Mirai-based malware botnet is spreading through a 5-year-old remote code execution (RCE) zero-day in AVTECH IP cameras, which have been discontinued for years and will not receive a patch.
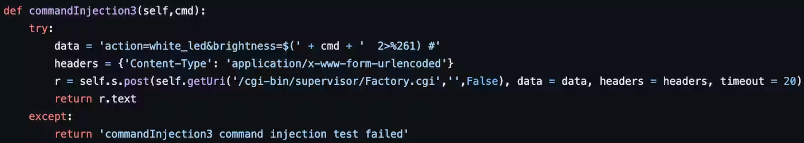
The flaw, discovered by Akamai’s Aline Eliovich, is tracked as CVE-2024-7029 and is a high-severity (CVSS v4 score: 8.7) issue in the “brightness” function of the cameras, allowing unauthenticated attackers to inject commands over the network using specially crafted requests.
Specifically, the easy-to-exploit flaw lies in the “brightness” argument in the “action=” parameter of the AVTECH cameras’ firmware, intended to allow remote adjustments to the brightness of a camera.
The flaw impacts all AVTECH AVM1203 IP cameras running on firmware versions up to Fullmg-1023-1007-1011-1009.
Due to the impacted models no longer being supported by the Taiwanese vendor, having reached their end of life (EoL) in 2019, no patch is available to address CVE-2024-7029, and no fixes are expected to be released.
The U.S. Cybersecurity and Infrastructure Security Agency released an advisory at the start of the month to warn about CVE-2024-7029 and the availability of public exploits, warning that the cameras are still used in commercial facilities, financial services, healthcare and public health, and transportation systems.
Proof of concept (PoC) exploits for the particular flaw have been available since at least 2019, but a CVE was only assigned this month, and no active exploitation had been observed previously.
Exploitation underway
Corona is a Mirai-based variant that has been around since at least 2020, exploiting various vulnerabilities in IoT devices to propagate.
Akamai’s SIRT team reports that starting on March 18, 2024, Corona began leveraging CVE-2024-7029 in attacks in the wild, targeting AVM1203 cameras still in service despite them having reached EoL five years ago.
The first active campaign we observed began on March 18, 2024, but analysis showed activity for this variant as early as December 2023. The proof of concept (PoC) for CVE-2024-7029 has been publicly available since at least February 2019, but it never had a proper CVE assignment until August 2024.
The Corona attacks, as those have been captured in Akamai’s honeypots, exploit CVE-2024-7029 to download and execute a JavaScript file, which, in turn, loads the primary botnet payload onto the device.
Once nested on the device, the malware connects to its command and control (C2) servers and awaits instructions on executing distributed denial of service (DDoS) attacks.
Other flaws targeted by Corona, according to Akamai’s analysis, are:
- CVE-2017-17215: A vulnerability in Huawei routers that allows remote attackers to execute arbitrary commands on the affected devices through the exploitation of improper validation in the UPnP service.
- CVE-2014-8361: A remote code execution (RCE) vulnerability in Realtek SDK, which is often found in consumer routers. This flaw can be exploited through the HTTP service running on these routers.
- Hadoop YARN RCE: Vulnerabilities within the Hadoop YARN (Yet Another Resource Negotiator) resource management system, which can be exploited to allow remote code execution on Hadoop clusters.
Users of AVTECH AVM1203 IP cameras are recommended to take them offline immediately and replace them with newer and actively supported models.
As IP cameras are commonly exposed to the internet, making them attractive targets for threat actors, they should always run the latest firmware version to ensure known bugs are fixed. If a device becomes discontinued, it should be replaced with newer models to continue receiving security updates.
Furthermore, default credentials should be changed to strong and unique passwords and they should be separated from critical or production networks.



