
Android malware “FakeCall” now reroutes bank calls to attackers
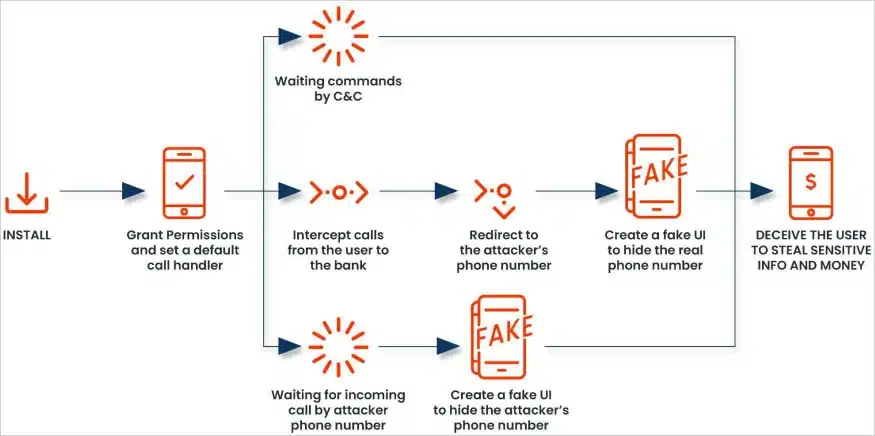
A new version of the FakeCall malware for Android hijacks outgoing calls from a user to their bank, redirecting them to the attacker’s phone number instead.
The goal of the latest version remains to steal people’s sensitive information and money from their bank accounts.
FakeCall (or FakeCalls) is a banking trojan with a focus on voice phishing, in which victims are deceived through fraudulent calls impersonating banks, asking them to convey sensitive information.
Kaspersky first reported the trojan in April 2022, featuring realistic-appearing calling interfaces to trick victims into believing they are on a call with their bank.
A March 2023 report by CheckPoint warned that FakeCall was now impersonating over 20 financial organizations, offering targets low-interest loans, and featuring new evasion mechanisms to lower detection rates.
In addition to vishing (voice phishing), FakeCall could also capture live audio and video streams from the infected devices, allowing attackers to steal sensitive data without victim interaction.
Hijacking calls
In previous versions, FakeCall prompted users to call the bank from within an app, impersonating the financial institute. Then, a fake screen was overlaid that displayed the bank’s actual number while the victim was connected with the scammers.
In the latest version analyzed by Zimperium, the malicious app sets itself as the default call handler, asking the user to approve this action upon installing the application through an Android APK.
The call handler in Android manages incoming and outgoing calls, essentially serving as the main interface that processes dialing, connecting, and ending calls.
When the malware prompts the user to set it as the default call handler, it gains permission to intercept and manipulate both outgoing and incoming calls.
A fake call interface mimics the actual Android dialer, displaying trusted contact information and names, elevating the level of deception to a point that’s hard for victims to realize.
What makes this malware so dangerous is that when a user attempts to call their financial institution, the malware secretly hijacks the call and redirects it to an attacker’s phone number instead.
“When the compromised individual attempts to contact their financial institution, the malware redirects the call to a fraudulent number controlled by the attacker,” explains the new Zimperium report.
“The malicious app will deceive the user, displaying a convincing fake UI that appears to be the legitimate Android’s call interface showing the real bank’s phone number.”
“The victim will be unaware of the manipulation, as the malware’s fake UI will mimic the actual banking experience, allowing the attacker to extract sensitive information or gain unauthorized access to the victim’s financial accounts.
New features and improvements
Despite heavier code obfuscation, Zimperium also discovered that the latest FakeCall versions add several improvements and attack mechanisms, though some are still under development.
First, FakeCall added a Bluetooth listener and a screen state monitor, both without malicious functionality yet.
The malware now leverages Android’s Accessibility Service to gain extensive control over the user interface, allowing it to monitor dialer activity, automatically grant itself permissions, and simulate user actions like clicks and gestures.
A new phone listener service establishes a communication channel with the attacker’s command and control (C2) server, allowing them to issue commands to perform various actions, like get device location, delete apps, record audio or video, and edit contacts.
New commands added on the latest variant include:
- Configure the malware as the default call handler.
- Start live streaming of the device’s screen content.
- Take a screenshot of the device display.
- Unlock the device if it’s locked and temporarily turn off auto-lock.
- Use accessibility services to mimic the press of the home button.
- Delete images specified by the C2 server.
- Access, compress, and upload images and thumbnails from storage, specifically targeting the DCIM folder for photos.
These additions show that FakeCall is under active development, and its operators are working towards making it a more evasive and formidable banking trojan.
Zimperium has published a list of indicators of compromise (IoC), including app package names and APK checksums so users can avoid the malicious apps that carry the malware. However, these are frequently changed by the threat actors.
As always, it is suggested that users avoid manually installing Android apps through APKs and instead install them from Google Play. While malware can still make it onto Google’s service, when detected, it can be removed by Google Play Protect.



