Crypto-stealing malware posing as a meeting app targets Web3 pros
Cybercriminals are targeting people working in Web3 with fake business meetings using a fraudulent video conferencing platform that infects Windows and Macs with crypto-stealing malware.
The campaign is dubbed “Meeten” after the name commonly used by the meeting software and has been underway since September 2024.
The malware, which has both a Windows and a macOS version, targets victims’ cryptocurrency assets, banking information, information stored on web browsers, and Keychain credentials (on Mac).
Meeten was discovered by Cado Security Labs, which warns that threat actors constantly change names and branding for the fake meeting software and have previously used names like “Clusee,” “Cuesee,” “Meetone,” and “Meetio.”
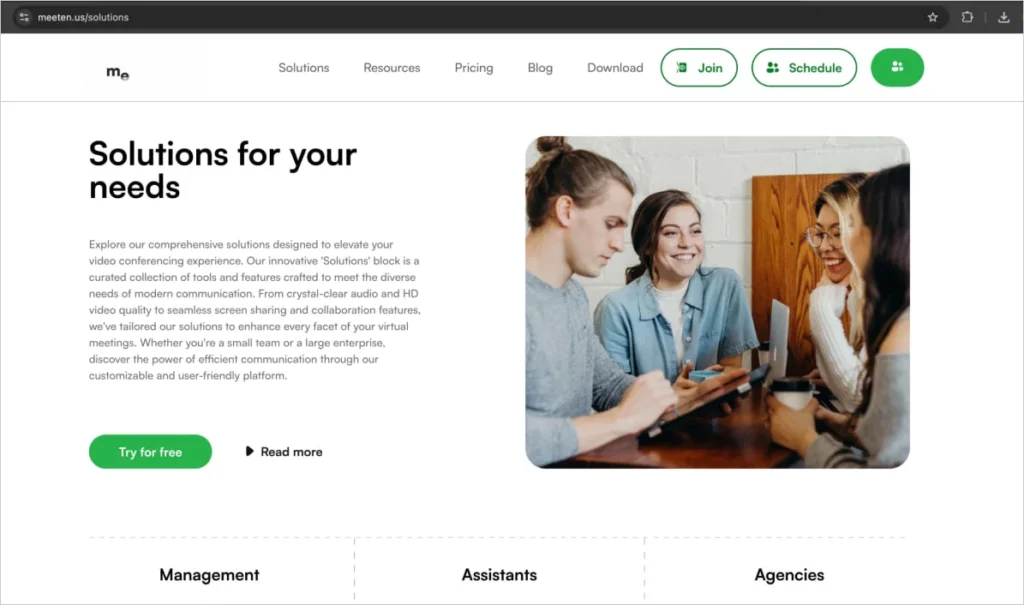
These fake brands are backed by seemingly official websites and social media accounts populated with AI-generated content to add legitimacy.
Visitors end up on the site through phishing or social engineering and are prompted to download what is supposedly a meeting application but, in reality, it is Realst stealer.
“Based on reports from targets, the scam is conducted in multiple ways. In one reported instance, a user was contacted on Telegram by someone they knew who wanted to discuss a business opportunity and to schedule a call. However, the Telegram account was created to impersonate a contact of the target. Even more interestingly, the scammer sent an investment presentation from the target’s company to him, indicating a sophisticated and targeted scam. Other reports of targeted users report being on calls related to Web3 work, downloading the software and having their cryptocurrency stolen.
After initial contact, the target would be directed to the Meeten website to download the product. In addition to hosting information stealers, the Meeten websites contain Javascript to steal cryptocurrency that is stored in web browsers, even before installing any malware.”❖ Cado Security
In addition to the Realst malware, Cado says the “Meeten” websites host JavaScript that attempts to drain wallets that connect to the site.
Targeting Macs and Windows
People choosing to download the macOS version of the meeting software get a package named ‘CallCSSetup.pkg,’ but other filenames have also been used in the past.
When executed, it uses the macOS command-line tool ‘osascript’ to ask the user to enter their system password, leading to privilege escalation.
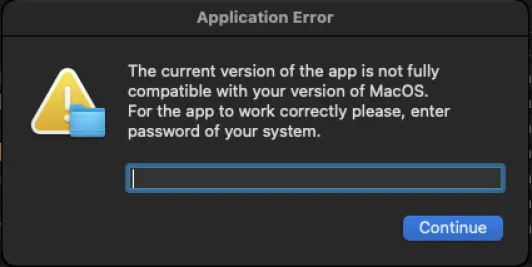
After entering the password, the malware will display a decoy message stating, “Cannot connect to the server. Please reinstall or use a VPN.”
However, in the background, the Realst malware steals data hosted on the computer, including:
- Telegram credentials
- Banking card details
- Keychain credentials
- Browser cookies and autofill credentials from Google Chrome, Opera, Brave, Microsoft Edge, Arc, CocCoc, and Vivaldi
- Ledger and Trezor wallets
The data is first stored locally in a folder, zipped, and eventually exfiltrated to a remote address along with machine details like build name, version, and system information.
The Windows variant of Realst is distributed as a Nullsoft Scriptable Installer System (NSIS) file, named ‘MeetenApp.exe,’ and it’s also digitally signed using a stolen certificate from Brys Software.
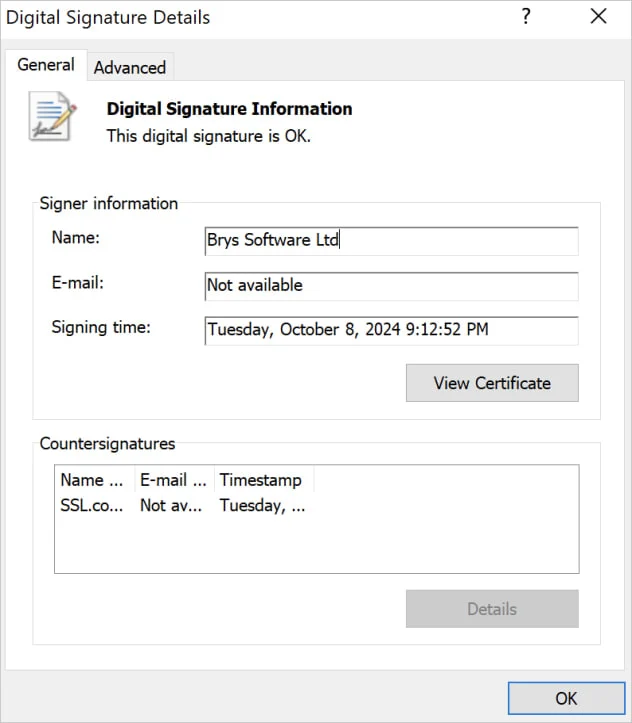
The installer contains a 7zip archive (“app-64”) and the core of an Electron application (“app.asar”) that contains JavaScript and resources, compiled using Bytenode into V8 bytecode to evade detection.
The Electron app connects to a remote server at “deliverynetwork[.]observer” and downloads a password-protected archive (“AdditionalFilesForMeet.zip) containing a system profiler (“MicrosoftRuntimeComponentsX86.exe”) and the main malware payload (“UpdateMC.exe”).
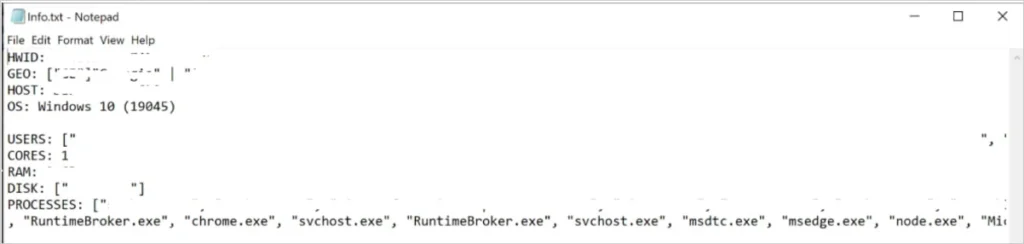
The Rust-based executable attempts to collect the following information, add it to a ZIP file, and exfiltrate it:
- Telegram credentials
- Banking card details
- Browser cookies, history, and autofill credentials from Google Chrome, Opera, Brave, Microsoft Edge, Arc, CocCoc, and Vivaldi
- Ledger, Trezor, Phantom, and Binance wallets
Compared to macOS, the Windows version features a more elaborate and versatile payload delivery mechanism, better evasion, and the ability to persist between reboots through registry modification.
Overall, users should never install software recommended by users through social media without first verifying if the software is legitimate and then scanning it on a multi-engine antivirus tool like VirusTotal.
Those working in Web3 are particularly vulnerable, as social engineering is a common tactic used to build a rapport with targets in this space, and then ultimately trick targets into installing malware to steal cryptocurrency.